Microsoft won’t patch SMBv1 vulnerability
With Petya and Wannacry ransomware on the loose, Microsoft urged Windows 10 users to remove SMBv1/CIFS file sharing protocol from their computers. Wannacry and Petya ransomware both use this vulnerability on port 445 to compromise Windows machines, inject malware and spread to other machines in the network.
If you still haven’t remove the SMBv1 protocol from your computer, Microsoft strongly advises you to do so, because future ransomware variants might take advantage of the same vulnerability.
Risksense discovered this vulnerability in June and reported this exploit to Microsoft, but the Redmond giant said that it won’t fix this flaw. Microsoft is planning to remove the SMBv1 protocol completely in the upcoming Windows 10 Fall Creators update, but there won’t be a patch for all previous versions of operating systems from Microsoft.
The huge problem lies in many users not being aware of the SMBv1 danger and that it had to be removed manually. In this particular case, Windows users are not protected just by regularly installing Windows updates and having Antivirus software installed.
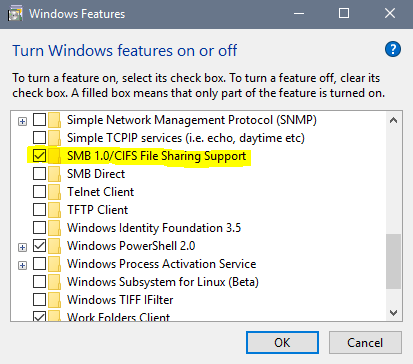
Here are the steps on how to deactivate SMBv1 from your Windows 10 machine:
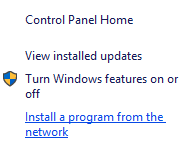
From the Start menu open Apps & Features
In the right pane, under Related settings select “Programs and Features”
In the left pane click on “Turn Windows features on or off”
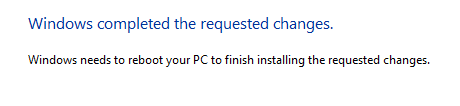
Scroll down to SMB 1.0/CIFS File Sharing Support and uncheck the checkbox, then click OK.Restart your machine.