Zero-day Adobe Flash Player vulnerability targets Microsoft Office documents
South Korean security researchers have released a warning about a new Adobe Flash zero-day vulnerability on the loose.
They claim that North Korean hackers are responsible for this hack targeting South Korean individuals who are researching North Korea. Adobe confirmed that all Flash versions including the latest available releases for Windows, Linux, and Mac are affected by this exploit. Once the system is infected, an attacker can gain full control of the target system.
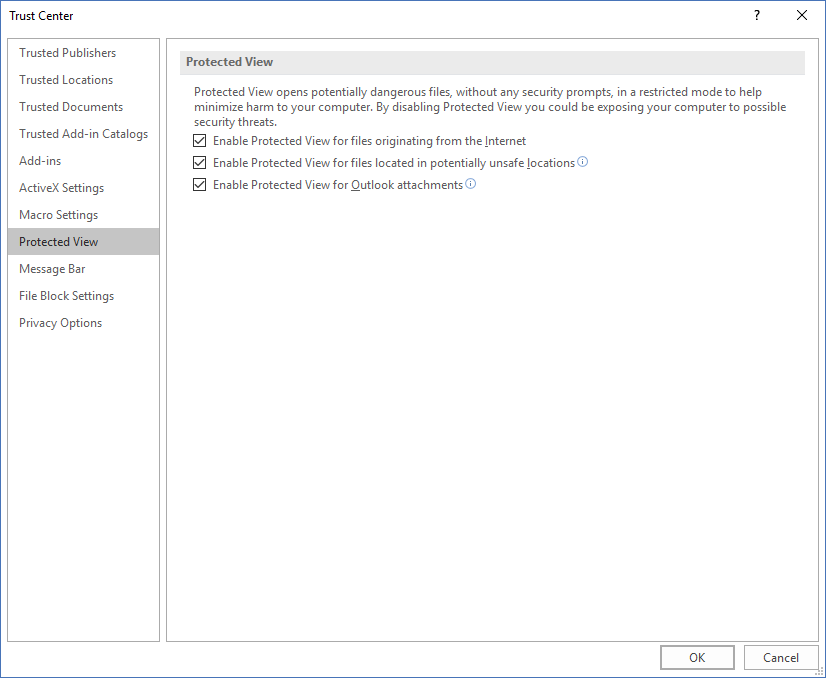
A general recommendation is not to open email attachments from unknown and suspicious sources. As of now, no patch is available although Adobe plans to release it during the next week. A security advisory was published by Adobe describing the CVE-2018-2878 flaw and advises users to enable Protected View so they’re opening documents in read-only mode.
“Protected View” for Microsoft Office should be enabled by default but if not here’s how you can check and enable it on your system.
Open Microsoft Word or any other Microsoft Office application.
Click on File | Options | Trust Center | Trust Center Settings | Protected View
Enable all checkboxes as per the picture below:
On the other hand, if you want to be perfectly sure that your system is not vulnerable to this attack it is recommended that you uninstall the Flash player from your system until the patch is released.